Oracle Extortion Incident Unfolds
Oracle Corporation confirmed on October 3 2025 that a cyberattack had targeted several enterprise customers. The Oracle Extortion campaign involves hackers claiming access to confidential data from Oracle’s E-Business Suite. They allegedly sent ransom demands, threatening to leak information unless paid. Oracle stated that its internal systems remain secure and that investigations are underway with global cybersecurity agencies.
Customer Impact and Attack Method
According to Oracle’s preliminary findings, the Oracle Extortion attackers exploited weak authentication through social engineering. They stole configuration files and credentials before launching extortion emails. Unlike ransomware that encrypts data, this campaign centers on theft and exposure. Security experts note that victims may not immediately detect the breach, making it more dangerous. The attack also reflects how extortion groups are evolving to bypass endpoint defenses and exploit cloud dependencies.
Industry Reactions and Analyst Warnings
The Oracle Extortion case has drawn broad attention from enterprise security analysts. Many say it highlights growing risks tied to cloud and third-party integrations. Researchers suggest attackers used dark-web data to identify Oracle clients, enabling customized extortion messages. Analysts recommend organizations adopt zero-trust frameworks and enforce stronger identity verification measures to reduce exposure to similar threats.
Oracle’s Strategic Response Plan
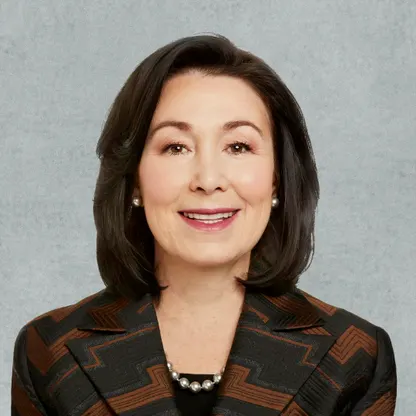
To address the incident, Oracle has activated a multi-phase response strategy. It urged customers to reset passwords, enable multi-factor authentication, and review network access. Updated Oracle Cloud Guard policies are being deployed to detect abnormal behavior. Mary Hannon, Oracle’s Chief Information Security Officer, confirmed that Oracle’s production systems remain unaffected. She added that transparency and rapid communication are central to Oracle’s containment strategy.
Enterprise Lessons from the Oracle Extortion Incident
For enterprises worldwide, the Oracle Extortion case reinforces the importance of cyber resilience and visibility across hybrid environments. Businesses must adopt real-time monitoring, identity governance, and secure data-sharing frameworks to counter evolving threats. Security teams should test incident-response playbooks and practice crisis communication in case of extortion attempts. As cyberattacks become more precise and targeted, proactive defense is now a boardroom-level priority rather than just an IT mandate.
Policy and Regulatory Response
In response to the Oracle Extortion report, regulators in the U.S. and Europe have requested details about customer impact. Industry bodies, including the Cloud Security Alliance, are advocating new compliance measures for vendor risk management. Policymakers argue that greater transparency on third-party controls is essential to preserve client confidence. The incident could accelerate efforts toward mandatory disclosure of extortion attacks and supplier breaches across regulated industries.
Global Takeaway
The Oracle Extortion breach is a stark reminder that even established technology vendors can become entry points for cybercriminals. Strengthening access controls, auditing partner integrations, and improving staff awareness remain crucial defense steps. In today’s interconnected environment, prevention relies on vigilance, cooperation, and shared intelligence across the cybersecurity ecosystem.